F5 BIG-IP ASM WAF Rules Report
Invicti scans your system to identify vulnerabilities that may have a critical or high severity level. If you cannot fix these vulnerabilities immediately, attackers may exploit them and take control of your website. Invicti helps prevent malicious hackers from attacking these vulnerable URLs in your system by allowing you to export rules for F5 BIG-IP Web Application Firewall (WAF).
By generating Invicti’s findings as F5 BIG-IP WAF Rules:
- You can immediately block requests to a resource if the requests contain malicious payloads that would exploit it
- Developers gain time in fixing these vulnerable points
- Your system remains secure until a fix is found and patched.
Please note that you cannot cover all security flaws by blocking access to a specific resource using a web application firewall. For example, application source code disclosure cannot be exported as a F5 BIG-IP WAF rule.
Both Invicti editions allow the export of scan results as F5 BIG-IP WAF Rules.
Click to view a sample Big-IP ASM WAF Rules Report.
For further information, see Overview of Reports, Report Templates, Built-In Reports, and Web Application Firewalls.
How to Generate an F5 BIG-IP ASM WAF Rules Report in Invicti Enterprise
- Log in to Invicti Enterprise.
- From the main menu, click Scans, then Recent Scans. The Recent Scans window is displayed.
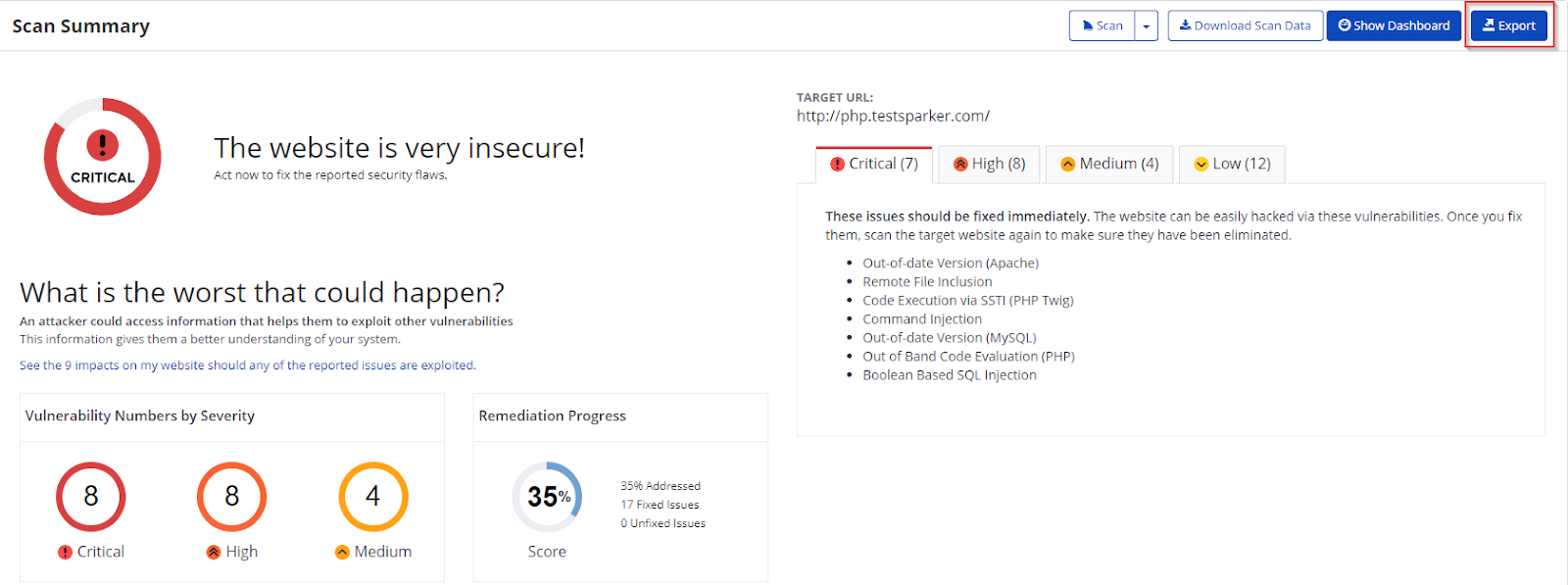
- Next to the relevant report, click Report. The Scan Summary window is displayed.
- Click Export. The Export Report dialog is displayed.
- From the Report dropdown, select F5 BIG-IP ASM WAF Rules.
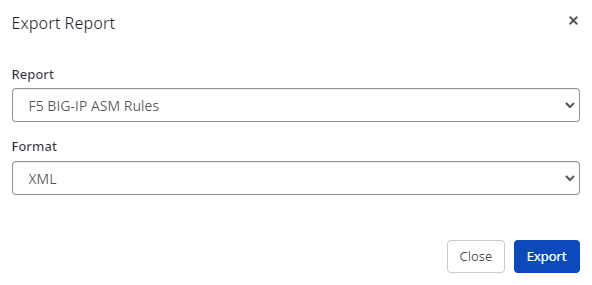
- From the Format drop-down, select an option.
- Click Export. You can view the report in the Save location.
How to Generate an F5 BIG-IP ASM WAF Rules Report in Invicti Standard
- Open Invicti Standard.
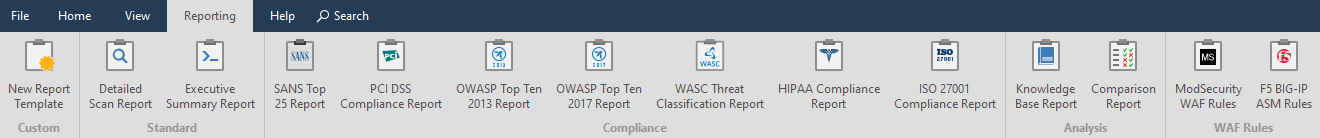
- From the Reporting tab, click the F5 BIG-IP ASM WAF Rules. The Save Report As dialog box is displayed.
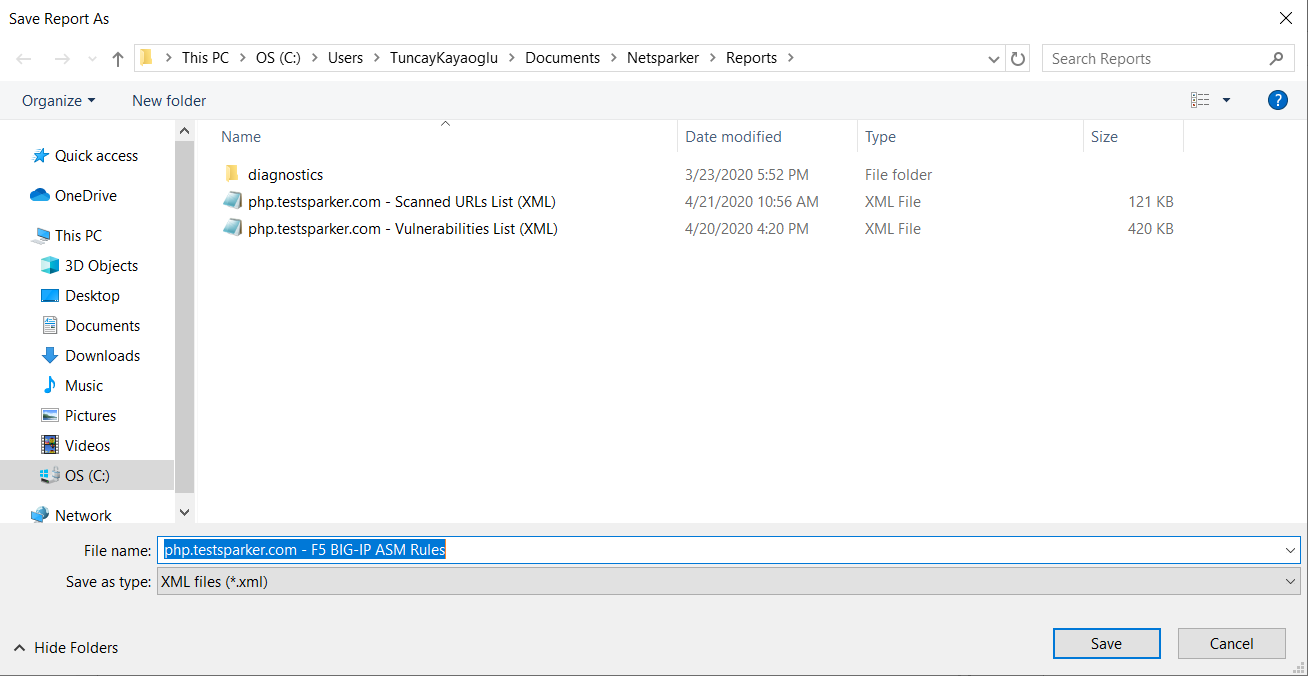
- Select a save location and click Save.
- The Export Report dialog is also displayed at this point, with the Path field already populated from the previous dialog.
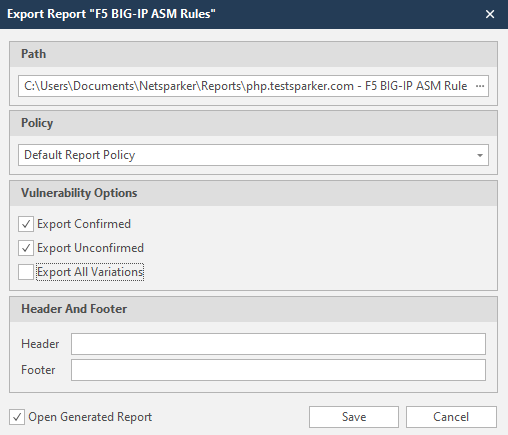
- From the Export Report dialog, you can decide on:
- Policy: Select the default policy or customized policy report (see Custom Report Policies).
- Vulnerability Options: Select all or any options below:
- Export Confirmed: When selected, the report will include confirmed vulnerabilities.
- Export Unconfirmed: When selected, the report will also include unconfirmed vulnerabilities.
- Export All Variations: Variations mean that if Invicti identified some passive or information level issues in more than one page, it does not show all these variations. However, users can change this by enabling or disabling this option.
- Header and Footer
- Enter relevant information that will appear in the header and footer section of the report.
- Open Generated Report: When selected, your report is generated when you click Save.
- Click Save.
