
Automate and Scale Your Web Security with Invicti
Invicti is a web vulnerability management solution that focuses on scalability, automation, and integration. Based on a leading-edge web vulnerability scanner, the Invicti platform uses proprietary Proof-Based Scanning technology to identify and confirm vulnerabilities, confidently indicating results that are definitely not false positives. Invicti is highly effective both integrated within the SDLC and as a standalone solution.

I’ve long been an advocate of Invicti because I believe it’s the easiest on-demand, do it yourself dynamic security analysis tool.
MICROSOFT REGIONAL DIRECTOR & MVP, FOUNDER OF HAVE I BEEN PWNED, LEADING SECURITY RESEARCHER
Integrate the Invicti Web Vulnerability Scanner within Your SDLC
Web application security testing tools in complex environments should work together seamlessly with existing systems. You can integrate Invicti with market-leading CI/CD solutions and issue trackers to use the web application security scanner in your DevSecOps/SecDevOps environment and follow the best practice shift-left paradigm (test early and test often). Such an approach will let you eliminate security vulnerabilities as early as possible, helping you save a lot of resources. You can also easily use Invicti together in the SDLC with other security tools, for example, source code analyzers.

Achieve Full Web Application Development Scalability with Proof-Based Scanning
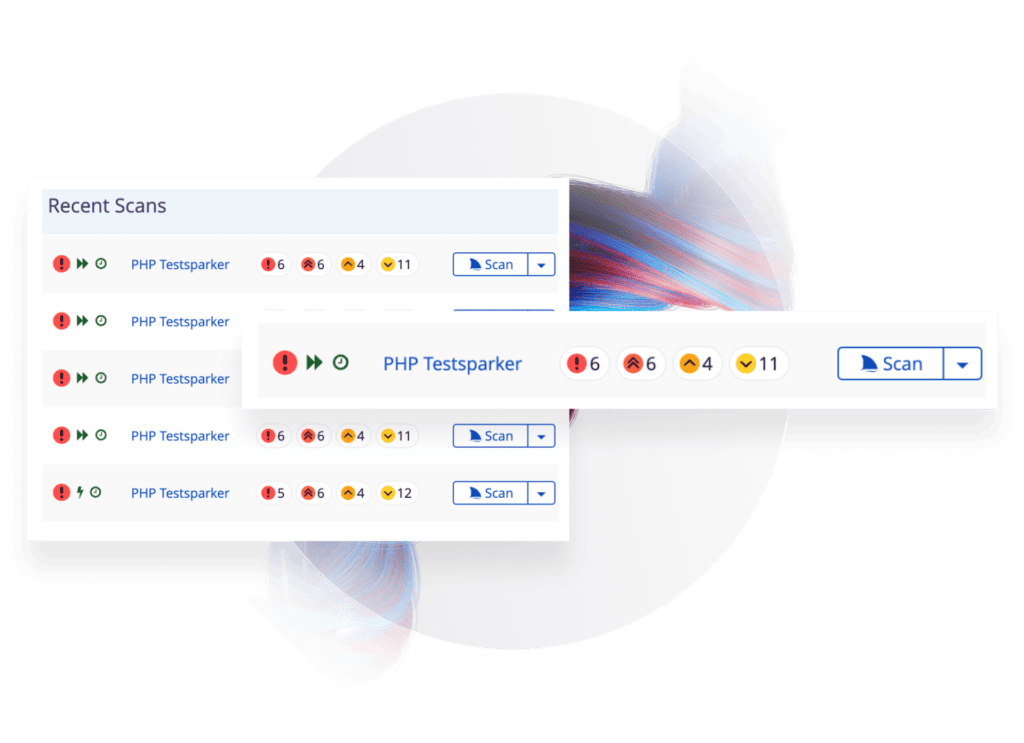
Invicti automatically exploits identified website security vulnerabilities in a safe way and also produces a proof of exploitability. Therefore, you can immediately see the impact of the web application vulnerability and be sure it is not a false positive, so you do not have to waste time on manual penetration testing to verify scan results. False positives are the leading cause of scalability problems for other web application scanners. This unique technology helps you make your vulnerability scanning processes fully scalable.
Find More Vulnerabilities with the Industry-Leading Website Vulnerability Scanner Engine
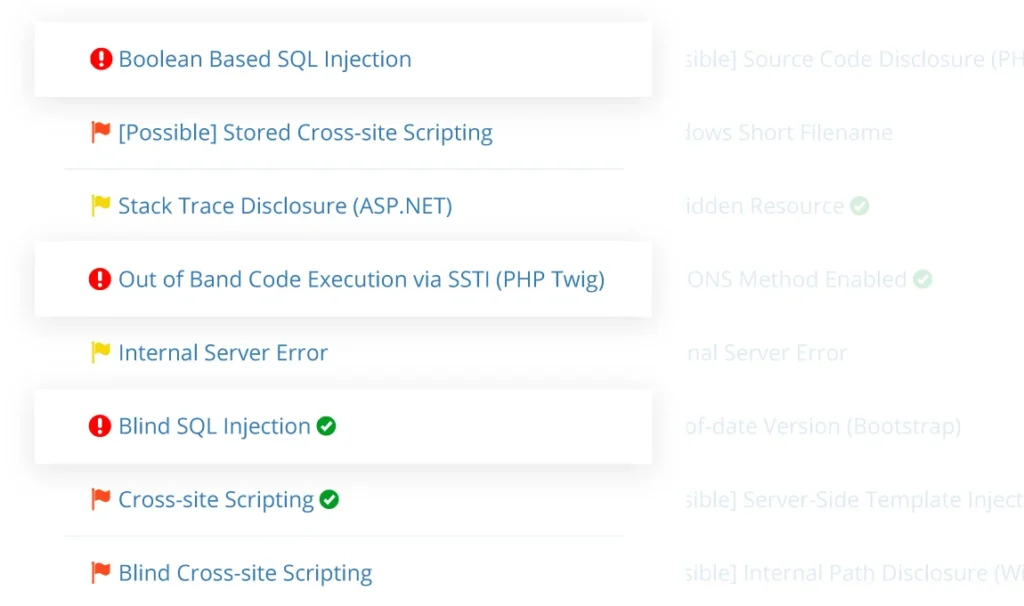
Both the on-premises and hosted editions of the Invicti security scanner use a unique black-box (DAST) scanning technology that finds more security vulnerabilities than any other web application vulnerability scanners, as proven by independent comparisons with similar scanning tools. Invicti is optimized to handle even the most complex applications based on JavaScript/Ajax. The scanner identifies thousands of OWASP Top 10 vulnerabilities in web pages, web applications, web services, and APIs, such as SQL injections, cross-site scripting (XSS), directory traversal, command injection, remote file inclusion, and more. Invicti also checks the web server, running server configuration tests for commercial and open-source web servers such as Apache and Nginx on Linux, and IIS on Microsoft Windows, to ensure there are no misconfigurations that might lead to security issues.
Trusted by IT & Telecom Companies Like








“Invicti are not just another vendor from where we purchase any other software, they are like business partners.”
Jade Ohlhauser, CTO
RPM Software Uses Invicti to Ensure their Online Service Offering is Secure
As a cloud-based software developer and provider, RPM Software is responsible for the sensitive data their customers store on their solutions, hence they cannot afford to take web application security lightly…
Featured IT & Telecom Content
Web Security
Does having a PCI compliant website and business means they are bulletproof, or better, hacker proof? This first part of this PCI compliance article looks into…
PCI Vulnerability Scan
Run automated PCI DSS vulnerability scans with Invicti to automatically identify security vulnerabilities in your web applications, and fix them to…
Web Security
As we have seen in part 1 of PCI Complaince, the Good, the Bad and the Insecure, PCI compliance is a good idea in abstract, however it should be…
Web Security
When it comes to compliance, especially as it relates to web application security, the Payment Card Industry Data Security Standard (PCI DSS) is usually the main…
IT Security Software Tools
Businesses are focusing on web security to ensure the web & cloud based services they use are secure. Web application security is not easy…
Server Security Software
An accurate and automated web server security software is vital to the security of your web applications, because the web server itself also needs to be secured…
