Save time and money with your own online vulnerability scanner
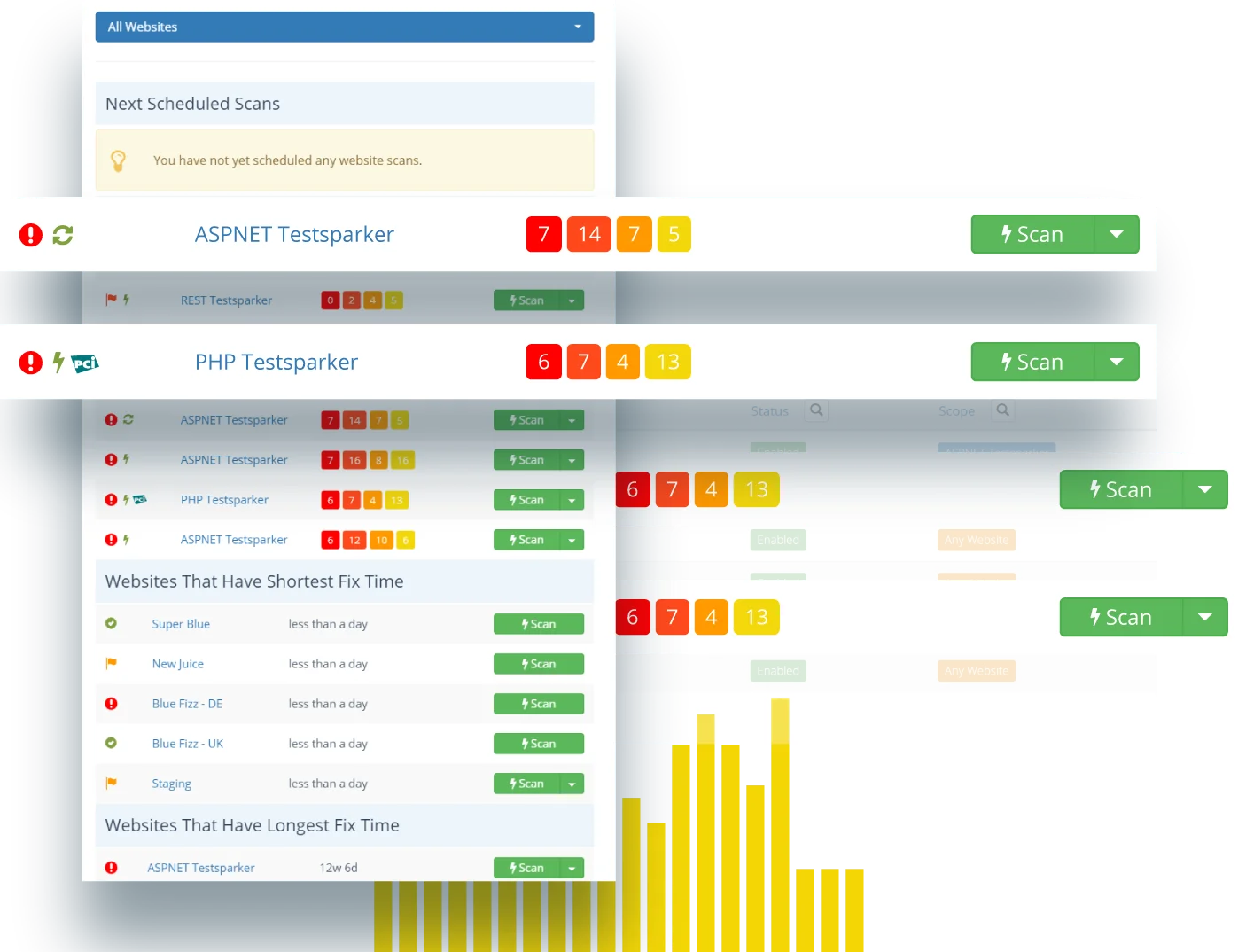
Reduce application security risk and save on external penetration testing by bringing your web vulnerability scanning in-house with Invicti’s scalable and automated web application security testing solution.

I’ve long been an advocate of Invicti because I believe it’s the easiest on-demand, do it yourself dynamic security analysis tool.
MICROSOFT REGIONAL DIRECTOR & MVP, FOUNDER OF HAVE I BEEN PWNED, LEADING SECURITY RESEARCHER
Cover all your in-house and third-party web apps and APIs
An accurate web vulnerability scanner is a crucial security tool to probe your entire attack surface and fix security flaws before malicious hackers can find and exploit them. Invicti Enterprise provides an on-demand SaaS platform for running cloud-based vulnerability tests across all your web applications and APIs. In addition to identifying vital OWASP Top 10 security vulnerabilities such as SQL injections and cross-site scripting (XSS), Invicti also protects your web server by checking for misconfigurations. The security scanner also checks for security issues in any third-party products, including open-source PHP-based CMS solutions like WordPress. As a dynamic application security testing (DAST) solution, Invicti can check for website vulnerabilities regardless of the back-end technologies powering your websites, applications, and APIs.


Fix issues faster by integrating web application scanning into DevOps
The real goal of vulnerability scanning is remediation, and that means reporting security issues to developers. In large enterprise environments with thousands of websites, applications, and API endpoints, the most efficient way to do this is to integrate website security scanning into your software development life cycle (SDLC) to create a DevSecOps ecosystem. Unlike many other vulnerability scanning tools, Invicti is specifically designed to be used in such workflows, with an industry-leading set of built-in integrations and a full internal API for custom deployments. Extensive automation includes the ability to create bug tickets from scan results directly in popular issue trackers and to trigger scans from CI/CD tools. You can also integrate with web application firewalls (WAFs) to temporarily block attacks until a vulnerability is fixed.
Eliminate noise and get rapid results with automated vulnerability confirmations
Invicti uses proprietary proof-based scanning technology to safely and fully automatically exploit many typical web vulnerabilities and provide evidence that they are real and not false positives. Coupled with hundreds of mature security checks that incorporate over a decade of cybersecurity expertise, this saves your teams hundreds of hours on manual verification and penetration testing. To maximize coverage and accuracy, the Invicti scanner uses a full embedded web browser engine to crawl and test any website or application, including JavaScript-heavy single-page applications. Support for industry-standard authentication methods (including SSO) allows for authenticated scanning of web pages and API endpoints to make sure everything is tested and you have all the facts you need to prioritize remediation.

What is a web vulnerability scanner?
A web vulnerability scanner is an automatic tool that examines websites and web applications from the outside and tests them for common security vulnerabilities like cross-site scripting (XSS), SQL injection, server-side request forgery (SSRF), and misconfigurations. Web vulnerability scanners are classified as dynamic application security testing (DAST) tools and are crucial for finding and fixing web security weaknesses before malicious hackers can exploit them.
Learn more about dynamic application security testing (DAST)
Who needs to use web vulnerability scanning?
Periodic web vulnerability scanning is a vital part of ensuring cybersecurity for any organization that runs websites, web applications, or APIs. In the past, vulnerability scanning was often performed only sporadically as part of penetration testing or vulnerability assessment. With most sizeable businesses now running large web environments that are frequently updated, regular vulnerability scanning is a major part of maintaining a good security posture.
Read more about the importance of systematic web vulnerability testing and management
Is a web vulnerability scanner the same as a network scanner?
Web vulnerability scanners such as Invicti are used to test websites, web applications, and API endpoints for vulnerabilities that malicious users could exploit using a web browser or another tool communicating over HTTP. Network scanners such as nmap are a different class of tools, used to probe networks for open ports to find vulnerable services and systems. A network vulnerability scanner is not designed to detect application vulnerabilities such as cross-site scripting (XSS) or SQL injection.
Learn about the differences between application security and network security
Is vulnerability scanning legal?
Any type of active scanning where the scanner sends probes or mock attacks to the asset being tested requires the permission of the owner. Organizations can and should run vulnerability scans on their own web environments (or entitle a third party to do it), but scanning a website, web application, or any other computer system without the owner’s knowledge and permission is illegal. In some jurisdictions, any unauthorized security testing (including using a vulnerability scanner) may be treated as a cyberattack, regardless of the ethical motivation.
Trusted by IT & Telecom Companies Like








“Invicti are not just another vendor from where we purchase any other software, they are like business partners.”
Jade Ohlhauser, CTO
RPM Software Uses Invicti Enterprise to Ensure their Online Service Offering is Secure
As a cloud-based software developer and provider, RPM Software is responsible for the sensitive data their customers store on their solutions, hence they cannot afford to take web application security lightly…
Featured IT & Telecom Content
Web Security
Does having a PCI compliant website and business means they are bulletproof, or better, hacker proof? This first part of this PCI compliance article looks into…
PCI Vulnerability Scan
Run automated PCI DSS vulnerability scans with Invicti to automatically identify security vulnerabilities in your web applications, and fix them to…
Web Security
As we have seen in part 1 of PCI Compliance, the Good, the Bad and the Insecure, PCI compliance is a good idea in abstract, however it should be…
Web Security
When it comes to compliance, especially as it relates to web application security, the Payment Card Industry Data Security Standard (PCI DSS) is usually the main…
IT Security Software Tools
Businesses are focusing on web security to ensure the web & cloud based services they use are secure. Web application security is not easy…
Server Security Software
An accurate and automated web server security software is vital to the security of your web applications, because the web server itself also needs to be secured…
