The Importance of Finding All Vulnerabilities on Your Web Applications
Although compliance is mandatory, a secure web application is more important. This article explains why website owners should focus on finding and fixing all possible vulnerabilities on their web applications, even if it means doing much more than PCI DSS compliance require.
Your Information will be kept private.
Your Information will be kept private.
 Many businesses understand that it’s important to properly manage their web application security. But in truth, it goes far beyond the need to simply “avoid being hacked”. There are often serious liabilities associated with the failure to properly manage your security.
Many businesses understand that it’s important to properly manage their web application security. But in truth, it goes far beyond the need to simply “avoid being hacked”. There are often serious liabilities associated with the failure to properly manage your security.
Unfortunately, many of those liabilities are an afterthought. Until of course, there is a security breach and it’s too late.
If you aren’t properly managing and implementing best practices, and even minimum compliance requirements, you could be putting the future of your business at risk.
In this post, we’re going to discuss the importance of scanning for, finding and removing all vulnerabilities within your web application. We’ll also tie this into the importance of complying with requirements such as PCI because these are often where the greatest liabilities exist.
Web Application Security and the Risk of Liability
A common question that tends to arise as a result of managing security vulnerabilities is whether or not the time and cost involved might provide a return on investment. Your initial inclination might be to look at the process of automated and manual security scanning as an expense, but that’s often not the case.
Although this makes sense from an accounting standpoint, you also need to consider the potential liabilities as a result of a security lapse.
For a small business, the result of a potential lawsuit could mean bankruptcy. Let’s take a quick look at a few examples:
As recently as January 2016, the New York Attorney General’s Office announced a settlement with Uber, under the terms of which, they agreed to pay a fine of $20,000 and change their security practices by protecting customer data. It’s small change for Uber, but a significant penalty for a small startup developing a web application.
At the other end of the spectrum, in late 2015, Wyndham Worldwide Corp. settled with the FTC and was required to implement a comprehensive security program after hundreds of thousands of customers had sensitive payment information exposed to hackers. Wyndham already had a security program in place, which obviously left at least one backdoor open. As a result of their breach, they now face 20 years of increased scrutiny. Imagine the added burden, both in terms of time and expense that your company would face as a result of a similar judgment.
The point I am trying to make is that you shouldn’t be looking at the security of your web application as an expense. Instead, consider the potential ROI that is achieved when you are able to thwart the most recent exploit in the wild. Being proactive is always the preferable choice.
Security Compliance is Not Enough
An organization like the PCI Security Standards Council helps to put standards in place to protect cardholder data around the world. The problem is, these PCI security standards are the minimum requirements in order to remain compliant. PCI DSS compliance is a great place to start, despite its nondescript nature. The fact remains that it only takes a single vulnerability to put thousands, or tens of thousands of your customers confidential information at risk.
Web Application vulnerabilities and exploits are constantly evolving. Any compliance standard put in place today could be out of date as early as tomorrow as a result of a new exploit. This alone makes compliance a minimum standard, not an acceptable level of achievement.
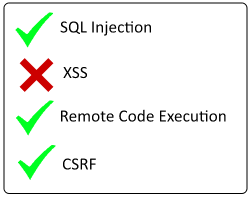
Again, a large-scale security breach requires but a single vulnerability – be it XSS, SQL injection or directory traversal. It’s simply not acceptable to be satisfied with finding “most” of the vulnerabilities in your web application – you need to find them all.
How You Can Find All Application Vulnerabilities
One of the risks of relying on standards such as PCI DSS is that is just because you are compliant, does not mean your application is secure. In contrast, if your web application is properly secured, you will have more confidence in your ability to maintain PDC DSS compliance. Although compliance is mandatory, a secure web application is more important.
It’s important to realize, is that there is no single solution capable of eliminating all web application security vulnerabilities. In almost all cases, effective scanning requires both automation and manual processes (ie. human assessment). An approved PCI ASV will use a combination of these two methods as well, necessitated by the complexity of today’s web applications. If your current method of assessing vulnerabilities consists of only one of these methods, you need to reassess your security practices.
Your Business Depends upon You Exposing All Vulnerabilities
There is no debating the importance of maintaining compliance standards. In the event of a negligent breach, the penalties can be financially severe and the consequences onerous, as seen in the examples above.
Beyond the compliance requirements, it’s equally important to consider the potential impact on the goodwill of your business. The trust of your customers is an intangible asset that can take years to earn. A security breach which puts their personal and confidential information at risk can cause irrevocable damage.
The most important point to understand is that a single vulnerability can expose you to an untold amount of risk. The process of properly scanning your web application for all vulnerabilities should considered a high ROI activity.






