Infographic: Statistics About the Security State of 104 Open Source Web Applications
In this infographic, we highlight the most common vulnerabilities that are found in open source web applications. Even though this is just a small sample of the web applications that are used on the live website on the internet, these statistics give us a good overview of the real life situation, and how many websites are vulnerable to malicious hacker attacks.
Your Information will be kept private.
Your Information will be kept private.
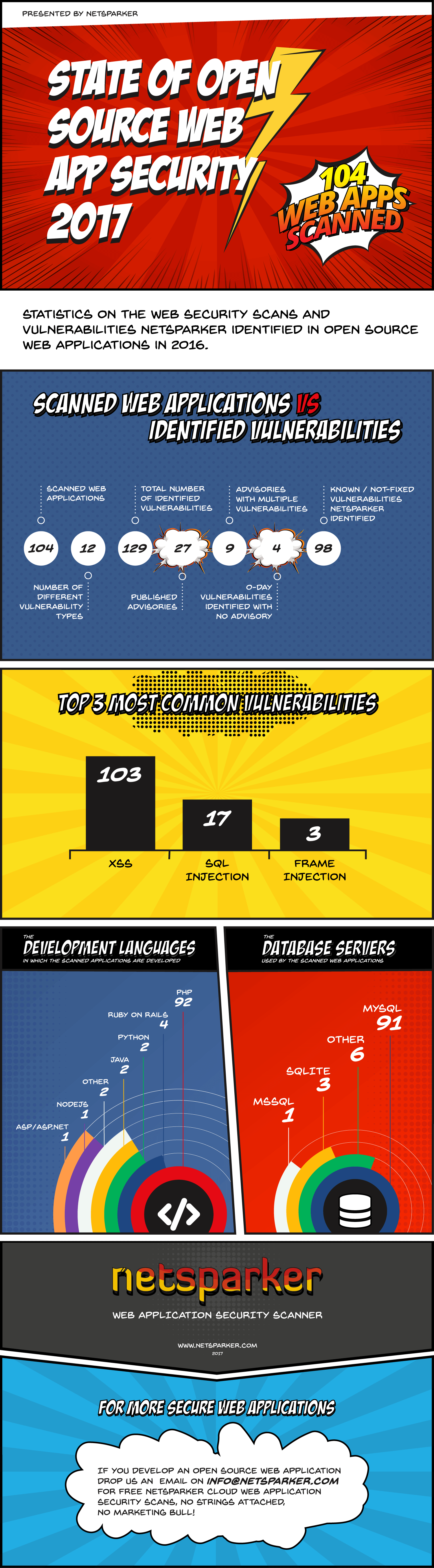 Every year we publish a number of statistics about the vulnerabilities which the Netsparker web application security scanner automatically identified in open source web applications. Netsparker is a heuristic web application security scanner, so all these vulnerabilities have been identified heuristically, and not with signatures. Here are the numbers for the scans and research we have done in 2016.
Every year we publish a number of statistics about the vulnerabilities which the Netsparker web application security scanner automatically identified in open source web applications. Netsparker is a heuristic web application security scanner, so all these vulnerabilities have been identified heuristically, and not with signatures. Here are the numbers for the scans and research we have done in 2016.
Why Do We Use Open Source Web Applications for Testing?
We use open source web applications to test our dead accurate web vulnerability scanning technology because of the diversity. You can find any type of web application you can dream of in the open source community; forum, blog, shopping cart, social network platform etc. You can also find applications written in almost all of the development languages available, such as PHP, Java, Ruby on Rails, ASP.NET etc. In fact, in 2016 we further diversified our test lab and included more web applications that are built with NodeJS, Python and other similar frameworks.
The other reason why we use open source web applications is because once we are doing the testing, we can still give something back to the community. By scanning these web applications and reporting the 0-day vulnerabilities back to the developers we are helping open source developers write more secure code.
In fact, we are so committed to helping open source projects developers, that we are also giving free Netsparker Enterprise accounts to all open source web developers.
Open Source Web Applications, Vulnerabilities & Numbers for 2016
How Many Web Applications and Vulnerabilities?
In 2016 we scanned 104 web applications and identified 129 vulnerabilities in 31 of them. Therefore 29.8% of the scanned web applications had one or more web application vulnerabilities in them.
How Many 0-Day Vulnerabilities Did Netsparker Identify?
During our test scans in 2016, we identified 31 0-day vulnerabilities, and we published 27 advisories, 6 of which were published in 2017. We do not always publish an advisory because it is not always possible to do so. Unfortunately, sometimes there are too many things that restrict us from publishing an advisory.
What About the Other Vulnerabilities?
The other 98 vulnerabilities that the Netsparker web vulnerability scanner identified were known vulnerabilities which have not been fixed yet. We keep a record of these vulnerabilities for two reasons:
- To measure the effectiveness of the automated scanner. I.e. if there are known vulnerabilities and the scanner does not identify them it means we are not doing a good enough job. The good news is that Netsparker did not just identify all the known vulnerabilities, but also uncovered 31 0-days.
- Even though these are known vulnerabilities, they have not been fixed in the latest version of the software in question. So anyone installing these web application will be vulnerable.
Are We Seeing More Secure Web Applications?
During both of 2015 and 2016, we published fewer advisories than we did in 2014. Does that mean that we are seeing more secure web applications? The answer is both yes and no.
Yes because some of the web application projects that have been around for years are becoming more secure. Their developers have more experience and are learning from the community. WordPress is a perfect example of this; WordPress core is very secure.
At the same time new open source web applications are being released almost on a daily basis, and even though it is not a guarantee, the chances of newly developed web applications having a vulnerability are very high. So there will always be a good number of vulnerable web applications out there.
Trivia: 26 of the scanned web applications were WordPress plugins, 8 of which had vulnerabilities.
Most Common Web Application Vulnerabilities in Open Source Web Applications for 2016
Which were the most common identified web application vulnerabilities in the open source web applications we scanned? Here are the numbers:
- XSS / cross-site scripting (reflected XSS, stored XSS, DOM XSS, blind XSS): 103
- SQL injection: 17
- Frame Injection: 3
- Open Redirection: 3
- HTTP Header Injection: 1
- Remote code execution: 1
- Cross-site Request Forgery / CSRF: 1
The top two culprits are cross-site scripting and SQL injection vulnerabilities, with XSS accounting for a staggering 81.9% of the identified vulnerabilities. This is not unusual, last year we had similar results with 180 XSS and 55 SQL Injection vulnerabilities.
Web Security Automation is the Key
According to the above numbers, on average a vulnerable web application would have 6.6 vulnerabilities. Malicious hackers are definitely happy with the a la carte selection of vulnerabilities they have at their disposal.
This is somehow expected considering the average modern web application has hundreds, if not thousands of possible attack surfaces. Web applications are becoming really complex and unless you automate security, it is impossible to develop a secure web application. Some people might not agree, but how can you, as a web application developer check that every possible attack surface on your web application is not vulnerable to hundreds of different vulnerability variants manually?
Definitely, you cannot and automation is the key here. That’s what we are focusing on at Netsparker. We do not just develop a scanner, but we are developing a web application security solution that generates dead accurate web security scan results, so you do not have to waste time manually verifying the findings.
Free Web Application Security Scans for Open Source Project
Take advantage of our offering and build more secure web applications. As an open source developer, you can get a free Netsparker Enterprise account so you can automatically scan your open source projects for web applications. Some open source projects such as OpenCart are already benefiting from free web application security scans.






